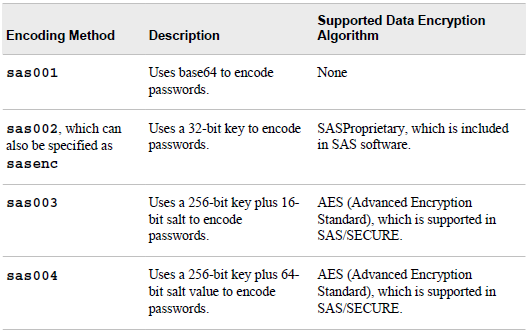
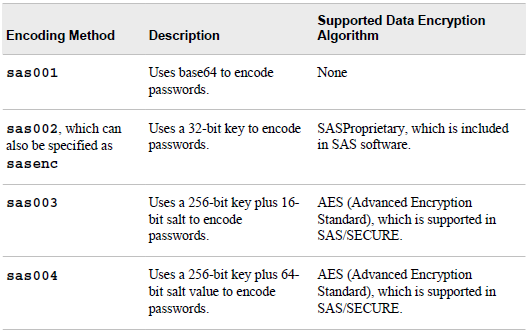
The code below lets you encode a password in SAS, based on the methods for encoding passwords available in SAS.
You can see a description of the methods for encoding below. Be aware that a password encoded with base64 (sas001) can be very easily discovered. See this blogpost of how to decode BASE64 directly in SAS.
Be aware of this website (Thanks Dmitriy for the comment below). That shows how to decode all passwords encoded with the above methods in SAS. And this older website, not showing the exact method but outlining the concept of how to do it.
If the website is not available, I have saved the webpage as pdf.
Encoding vs. encryption
PROC PWENCODE uses encoding to disguise passwords. With encoding, one character set is translated to another character set through some form of table lookup. Encryption, by contrast, involves the transformation of data from one form to another through the use of mathematical operations and, usually, a “key” value. Encryption is generally more difficult to break than encoding. PROC PWENCODE is intended to prevent casual, non-malicious viewing of passwords. You should not depend on PROC PWENCODE for all your data security needs; a determined and knowledgeable attacker can decode the encoded passwords.
Encoding is a process of converting one set of meaningful characters into another set. By converting into a different set the characters become unreadable and the meanings of the characters are disguised from the public.
Encryption is a method to transform data from plain text to cipher text through the use of a mathematical algorithmic scheme. Any plain text through encryption process becomes cipher text and is illegible to anyone without a special key.
Though both processes involve converting data from one format to another, encoding process is designed for disguising the data to be revealed casually. Encoding and decoding processes do not require a special key. On the other hand, encryption method is used to protect data from to be revealed to anyone other than the intended recipient. In order to read the encrypted text both the encryption key and the mathematical algorithm are required.
Encoding is intended to disguise data from to be revealed in public. For our purpose, it works well to prevent casual, non-malicious viewing of password in the SAS programs. Because of the special key and mathematical algorithm involved encryption is generally more difficult to break. It is designed for maintaining data confidentiality. Encoding and encryption are developed for different purposes. One should not replace another.
The code below saves a file to drive containing a %let statement with the encoded password.
%macro EncodePwd(SavePath, Method);
filename clp clipbrd;
proc pwencode in="&Password." out=clp method=&Method.;
run;
data _null_;
infile clp length=len;
length encodedPW $100;
input ;
encodedPW = substr(_infile_, 1, len); /* Remove linefeed */
call symput('encodedPW', compress(encodedPW));
run;
filename clp clear;
filename encoded "&SavePath.";
data _NULL_;
file encoded(pwd.sas);
tmp='%let pw='||"&encodedPW"||';';
put tmp;
run;
filename encoded clear;
%mend;
%EncodePwd(C:\, sas001);
%EncodePwd(D:\, sas002);